-
-
Notifications
You must be signed in to change notification settings - Fork 655
Report for Golang errors #284
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Conversation
65ea199 to
f05fd49
Compare
f05fd49 to
f7d6cdc
Compare
Right now if you use Gosec to scan invalid go file and if you report the result in a text, JSON, CSV or another file format you will always receive 0 issues. The reason for that is that Gosec can't parse the AST of invalid go files and thus will not report anything. The real problem here is that the user will never know about the issue if he generates the output in a file. I fix this problem in this patch and I added those Golang errors in the output. Signed-off-by: Martin Vrachev <[email protected]>
f7d6cdc to
d92962c
Compare
Codecov Report
@@ Coverage Diff @@
## master #284 +/- ##
=========================================
+ Coverage 55.84% 56.3% +0.45%
=========================================
Files 8 9 +1
Lines 462 492 +30
=========================================
+ Hits 258 277 +19
- Misses 182 188 +6
- Partials 22 27 +5
Continue to review full report at Codecov.
|
Signed-off-by: Martin Vrachev <[email protected]>
Signed-off-by: Martin Vrachev <[email protected]>
analyzer_test.go
Outdated
| _, _, golangErrors := analyzer.Report() | ||
| keys := make([]string, len(golangErrors)) | ||
| i := 0 | ||
| for key, _ := range golangErrors { |
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
should omit 2nd value from range; this loop is equivalent to for key := range ...
I added unit tests where I give an invalid file to Gosec. Also, I realized that is more logical if the line and the column attributes in the errors struct are integers. Signed-off-by: Martin Vrachev <[email protected]>
2122da1 to
759baed
Compare
There was a problem hiding this comment.
Choose a reason for hiding this comment
The reason will be displayed to describe this comment to others. Learn more.
This is great. Thanks!
|
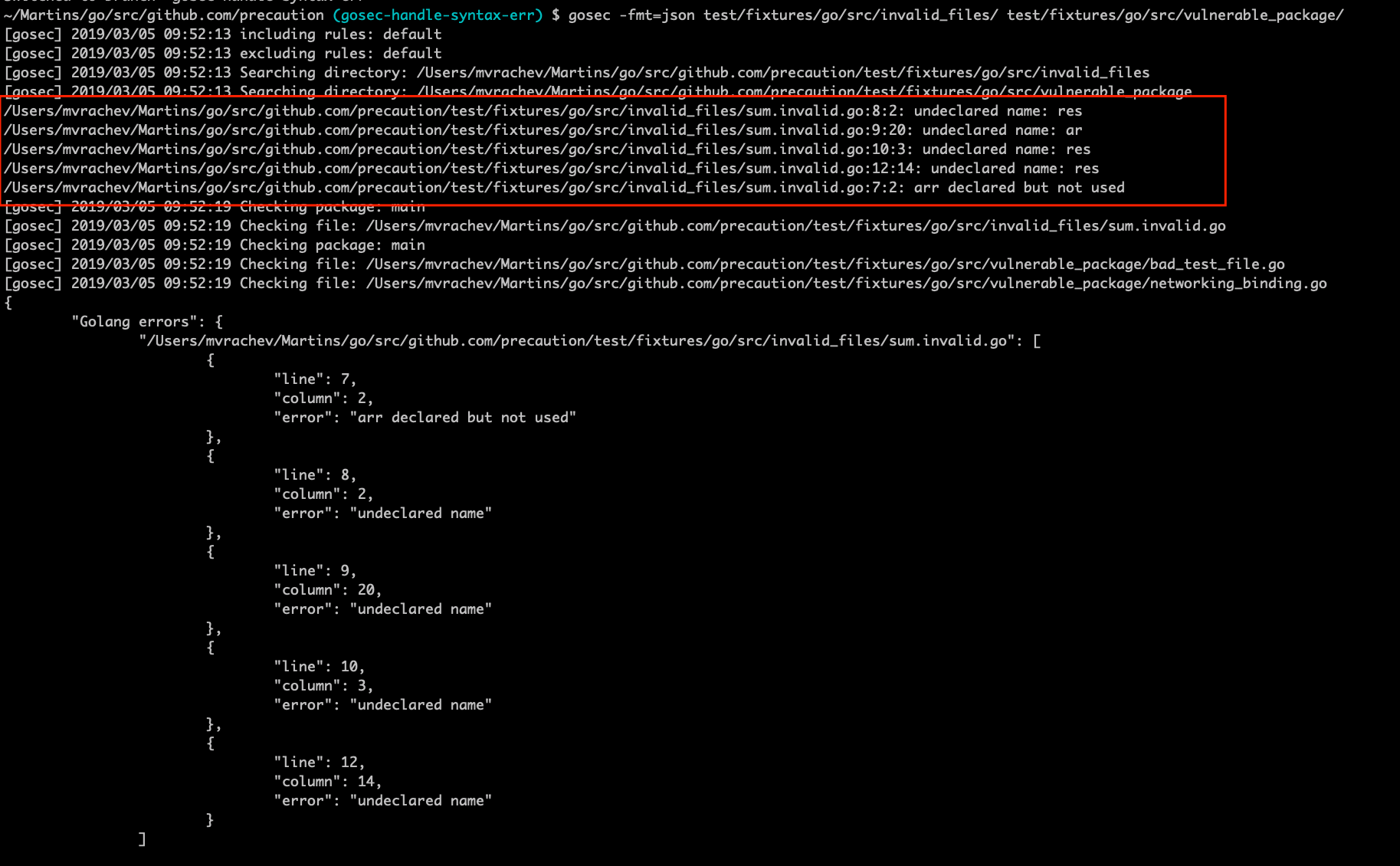
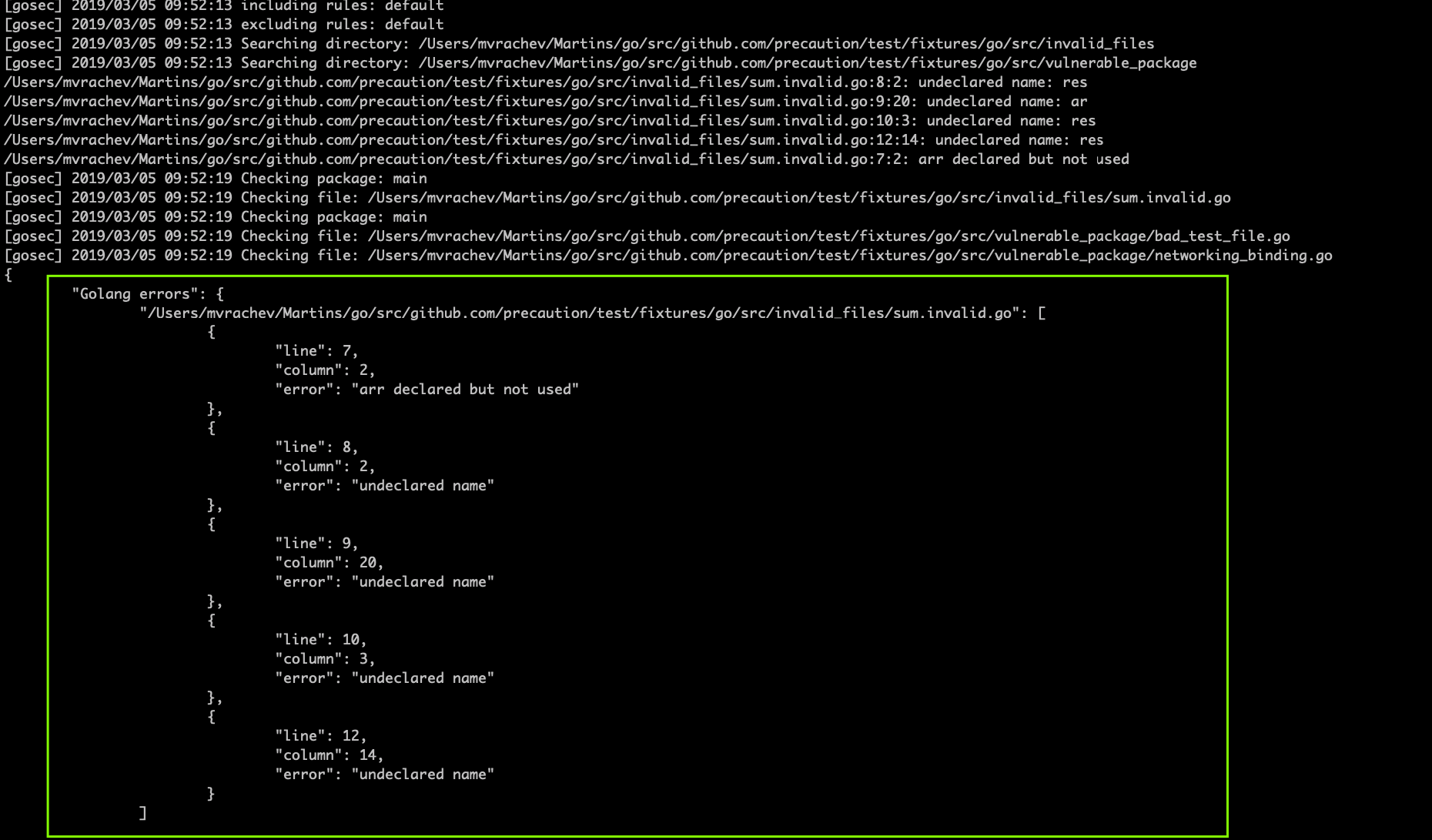
Great idea! But I wonder I get a bunch of errors from standard library files like: ... and many more lying in GOROOT. Do I have to exclude them? |
|
Red box :) |
|
Yes, you are right. That's something annoying from the golang parser library. I will try to look at this as soon as I can. |
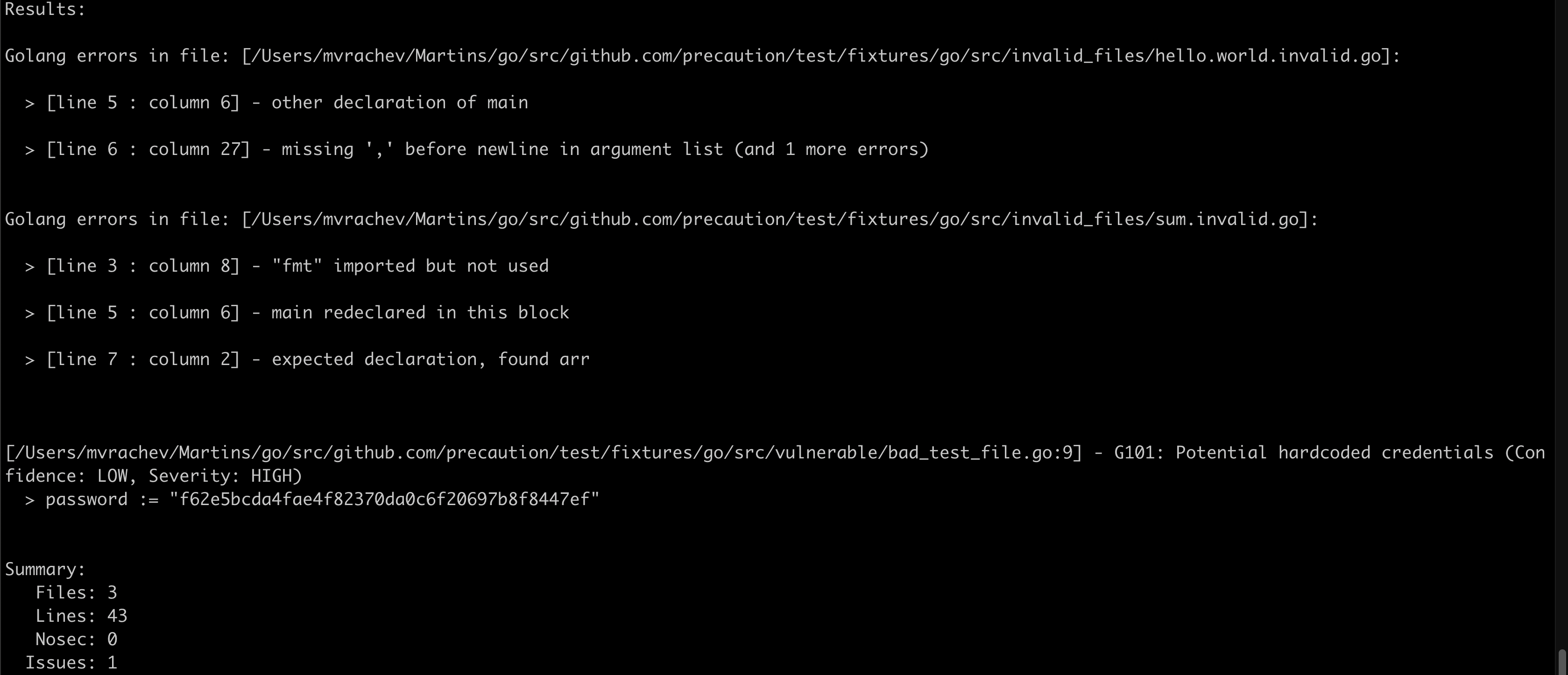
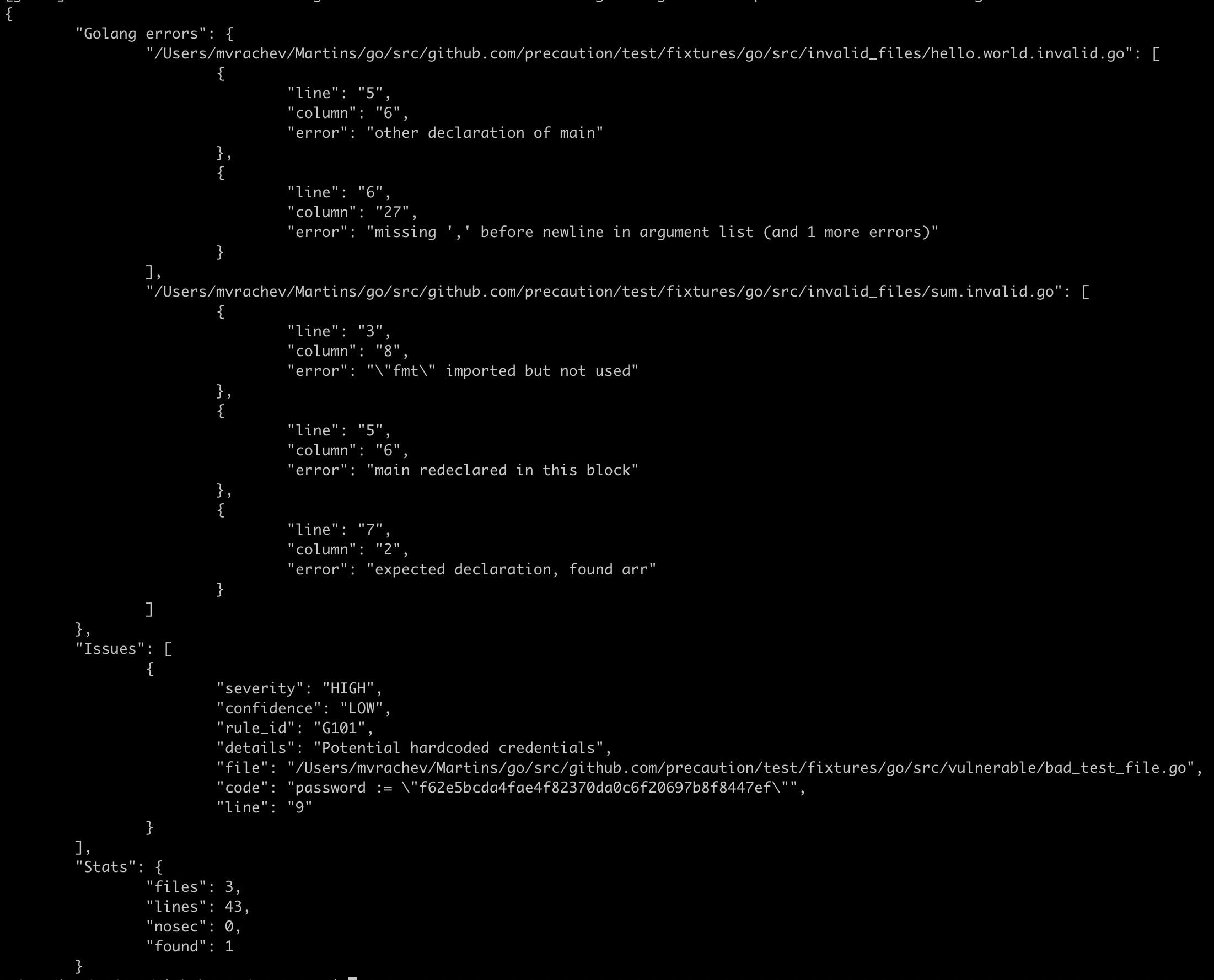
Right now if you use Gosec to scan invalid go file and if you report the result in a text, JSON, CSV or another file format you will always receive 0 issues.
The reason for that is that Gosec can't parse the AST of invalid go files and thus will not report anything.
The real problem here is that the user will never know about the issue if he generates the output in a file.
I fix this problem in this patch and I added those Golang errors in the output.
Now when there are Golang errors found Gosec will exit with code 1.
Signed-off-by: Martin Vrachev [email protected]